SSH
Jan 22, 2020 learning SSH PuTTY MobaXterm Linux
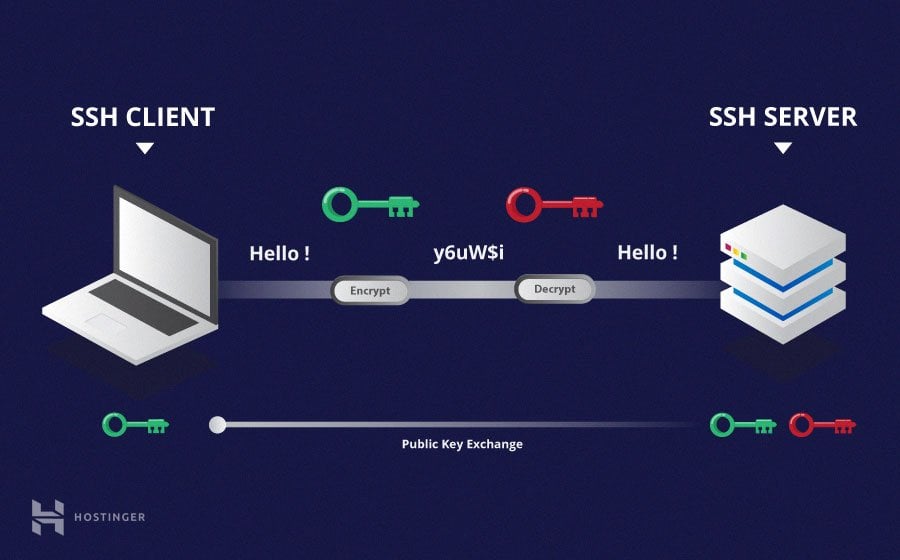
Figure taken from https://www.hostinger.com/tutorials/ssh-tutorial-how-does-ssh-work
SSH is the standard method to log into a remote Linux server. There is an SSH server program running in the remote machine monitoring any connection request from other machines. You can use an SSH client command or an SSH GUI to connect to that server:
$ ssh yourUserName@linux.server.name.or.ip
This is a lot of typing. If you log into the server frequently, you can reduce typing by saving some information in an ssh configuration file. If you don’t understand the syntax of the command above, please read Linux 101 first.
Configuration of SSH client
Command line configuration
$ cd # make sure that you are in your home directory
$ mkdir .ssh # make a hidden directory called .ssh
$ chmod 700 .ssh # make it only visible to yourself
$ cd .ssh
$ touch config # create an empty configuration file (only needed in MobaXterm)
$ open config # works in macOS and MobaXterm, use 'mimeopen config' in Linux
Please refer to chmod in wikipedia for detailed usage of chmod. Please read more about text editors, if you don’t know how to edit the config file.
The following is what’s inside of an example config file that specifies a short nickname, “l”, for server, “linux.server.name.or.ip”.
Host l
HostName linux.server.name.or.ip
User YourUserName
Now you can log into the Linux server by only typing
$ ssh l
GUI configurations
Two popular GUI SSH clients that work on Windows are
The default communication port for ssh is 22. It is set from the server side. If there is no specific instruction from your server administrator on the port number, it is mostly the default 22, there is no need for you to change it.
Copy files through SSH
Command-line method
$ scp localFile user@server:path/to/remote/copy #copy local file to remote machine
$ scp user@server:path/to/remote/file localCopy #copy remote file to local machine
$ scp user@server:/absolute/path/to/a/file localCopy #specify full path to a file
$ scp user@server:path/relative/to/your/home/directory/file localCopy
GUI programs
MobaXterm in Windows provides a nice side panel that shows files in the current folder in the terminal. One can drag files in and out of it for copying. Mac users may want to try https://cyberduck.io/, or https://filezilla-project.org/, or https://osxfuse.github.io/. Linux users can try SSHFS.
Edit remote files
Command-line methods
If you are an Emacs or Vim user, both editors provide commands to directly edit remote files.
GUI programs
Double click on a remote file shown in the MobaXterm side panel after you ssh into a remote machine, the file will be open in the MobaTextEditor. When you save your modification of the file, the updated version will be uploaded to the remote machine automatically. The same method works in Cyberduck and Filezilla.
Login without password
The easy way
Normally, a GUI SSH client can save your password to the server so that you don’t have to type it next time. This can also be achieved in the command line through a file called ~/.netrc. You can save your connection information (including the password) in this file:
$ touch ~/.netrc
$ chmod 600 ~/.netrc # hide it from others
$ open ~/.netrc # edit it, put the following into it:
machine remote.server.name.or.ip login username password sZ\#Je/j@3
The right way
Your password is saved as it is in ~/.netrc. A better way is to use SSH keys. The basic idea is that you generate a pair of keys, one is private, one is public. You upload the public one to the server and keep the private one secretly in your ~/.ssh. Next time, when you log into the server, if the two keys match, you will be logged in without typing in your password.
GUI through SSH
We can edit remote files using local editors as we described in the previous section. We can also use remote editors to edit remote files. Many editors can work inside a terminal, others create their own GUI, which have to be displayed in a X Window server.
Windows users can use MobaXterm, Xming, or Cygwin/X to establish an X Window server in your local PC. Mac users can use XQuartz.
Once your X Window server is running, you can let your ssh connection to the remote machine to send remote GUI program windows to your local machine and get displayed on your local X Window server:
$ ssh -X user@server # enable forwarding X connections through ssh
$ gedit remoteFile & # edit a remote file using a remote editor
To avoid typing -X every time, you can add the following line to your existing ~/.ssh/config:
ForwardX11 yes
VNC through SSH
There are two problems in using X-window. First, it is slow. Second, there is no free X-window server in iOS. We need VNC to overcome these problems.
VNC server
You can establish an VNC server in your remote machine following the steps below:
First, you need create a password for your VNC session using the following command:
$ vncpasswd
The password will be saved automatically in ~/.vnc/passwd.
Second, run
$ vncserver
to start an VNC session. The command may also create config, xstartup, a log file and a file containing the process id of the VNC session in ~/.vnc/. The VNC server will create an X Window server at the remote machine with a unique X DISPLAY number, which can be figured out by running
$ vncserver -list
TigerVNC server sessions:
X DISPLAY # PROCESS ID
:2 10949
The “:2” (including “:”) is the DISPLAY number. Your VNC session is running at port 5900 + the X DISPLAY number, i.e., 5902 in this concrete example.
Last, you can kill this session by
$ vncserver -kill :2
The X DISPLAY number cannot be ignored.
You can put some commands in ~/.vnc/xstartup, which will be run automatically when the VNC server starts. An example xstartup file would contain something like:
xterm # a terminal running in X Window
VNC client
RealVNC provides viewers for most operating systems. MobaXterm includes a VNC client as well:

These GUI programs provide intuitive interfaces to setup your VNC connection. If there is no space for you to specify the port, you can attach it to the end of the remote machine name:
remote.machine.name.or.id:5902
The port number must match the port number of your VNC server session.
SSH port forwarding
The problem is that an VNC port (590x) is normally not allowed to accept connections from other machines. We need ssh to be the middle man who forwards the connection request to that port through its encrypted connection line, which is called a tunnel. So ssh port forwarding is also called ssh tunneling. You can learn more about it at ssh.com and help.ubuntu.com. I personally like the explanation on stackexchange most.
The following command forwards server.ip.address:5902 to port 56783 in your own PC:
$ ssh -L 56783:127.0.0.1:5902 server.ip.address
The port number 56783 is chosen randomly. But there are some general suggestions on the right range of this number. The IP address 127.0.0.1 is called the loopback address. It is an address pointing to the machine itself, or the so-called localhost. In this example, 127.0.0.1 represents the same machine as server.ip.address.
Port forwarding can also be specified in the ssh config file:
LocalForward 56783 127.0.0.1:5902
After this, you need to make an ssh connection to the server to establish this tunnel. Now when you connect to port 56783 in your own machine, you are actually connected to port 5902 in the remote machine. Since the sole purpose of this connection is to establish the tunnel instead of doing any real work on your remote machine, you can turn on a few options of ssh:
$ ssh -fNT server.ip.address # run ssh in the background
Please man ssh to understand these options. To terminate a tunnel running in the background, use
$ pgrep ssh # find the process id of the running ssh tunnel
$ kill -9 pid # replace pid with the real process id given by the previous command
Port forwarding (MobaSSHTunnel) is also available under MobaXTerm’s tools menu. Another option in Windows to establish an ssh tunnel is to use PuTTY.
SSH jump host
There is an alternative to ssh port forwarding if you use MobaXterm’s VNC session setting:
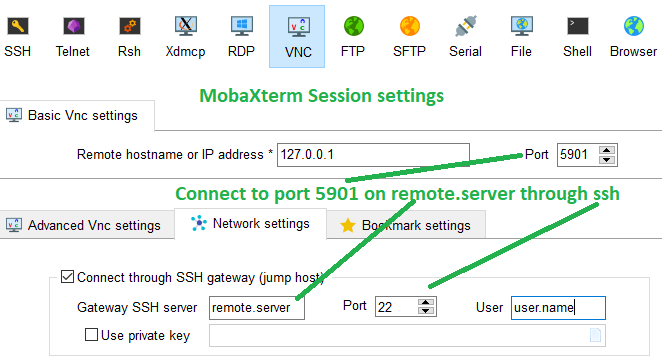
The CLI version of this method can be found in Gentoo wiki.
Window manager
When you establish a connection to the VNC session running on your remote machine through either ssh tunneling or jump host, you will be asked to type in the password you set for your VNC session using the vncpasswd command as mentioned in the previous session. After that, you should be able to see a terminal which does not even have a title bar to drag around. You need a type of programs called X window managers to achieve this simple action. Please refer to wikipedia for more information about the X window manager. Run one of the following commands in the terminal that you see in your VNC session to use one of the many X window managers:
- mwm (old fashion, fun to experience once)
- fluxbox (similar to Windows, simpler)
- dwm (A typical tiling window manager)
- gnome-shell (a modern one, more than just a window manager)
Activities mentions in this site have been supported by the following grants: